Technology
|
09 Jan 2022
物联网安全
保护您的客户和业务的关键。
尽管发挥了重要作用,但物联网应用存在于一个不断受到攻击的极其恶劣的环境中。为了让其能够充分发挥潜力,我们必须从第一天开始就解决物联网安全挑战。我们的五个安全支柱为强大且安全的互联解决方案提供了坚实的基础,以保护企业和终端用户免受物联网安全风险的影响。
什么是物联网安全?
物联网安全是指为保护物联网设备及其连接的网络而采取的一系列措施。无处不在的连接带来了新的风险。物联网安全曾经是一项希望具备的功能,如今已成为当今互联应用的基本要素。
由于物联网设备暴露于更广泛的互联网,物联网设�备开发人员必须时刻注意以下原则:
- 攻击总是造成伤害,包括:直接成本、损害和后果性成本。
- 应用中任何暴露的接口都可被用作攻击面。
保护物联网设备、保护数据和确保数据传输安全已成为构建可持续业务以应对日益增长的物联网安全威胁的首要任务。凭借强大的端到端安全措施,相关企业可以保护其收入,并通过保护设备和敏感数据降低与运营和声誉损害相关的成本。
物联网安全挑战
物联网设备不断暴露于各类型不断发展的物联网安全威胁中。最常见的类别包括:
- 数据窃取:如果物联网黑客能够访问易受攻击的设备,则就可以窃取敏感和潜在的机密数据,并将其在线出售给感兴趣的各方。
- 设备篡改:举例来说,业务赋能物联网设备(包括可通过篡改固件来修改系统行为的智能表计)可能会少报消耗量。
- 拒绝服务 (DoS) 攻击:黑客能够将大量物联网设备吸收到所谓的僵尸网络中以进行协同攻击,包括关闭网站。
- 未经授权的访问:如果安全性差,则联网的监控摄像头、门锁以及带有麦克风和其他传感器的物联网设备可能会被劫持。
- 勒索软件攻击:黑客可以锁定具有安全漏洞的物联网设备以中断相关公司的业务,直至收到赎金。
- 传感器欺骗:物联网设备可能会收到虚假信息,导致其出现故障。传感器欺骗涉及从复杂的射频信号干扰到简单的用硬纸板切口愚�弄摄像头的任何事项。
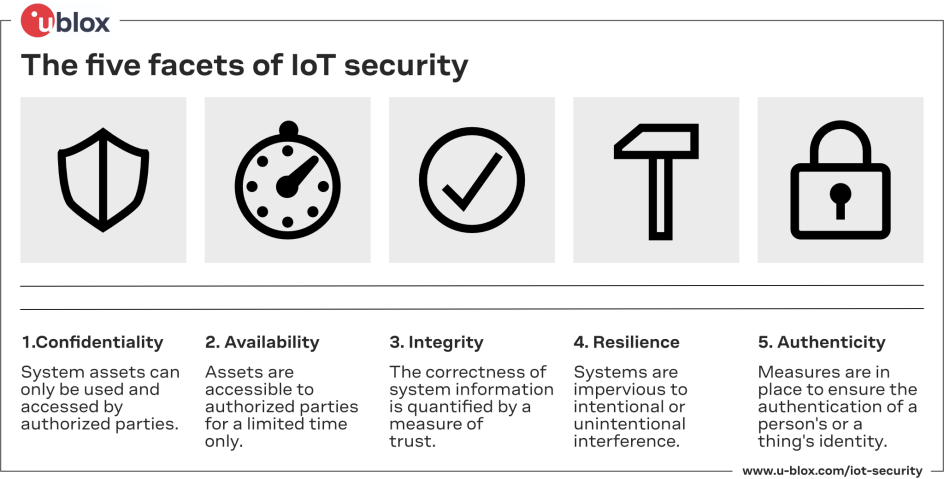
物联网安全的五个方面
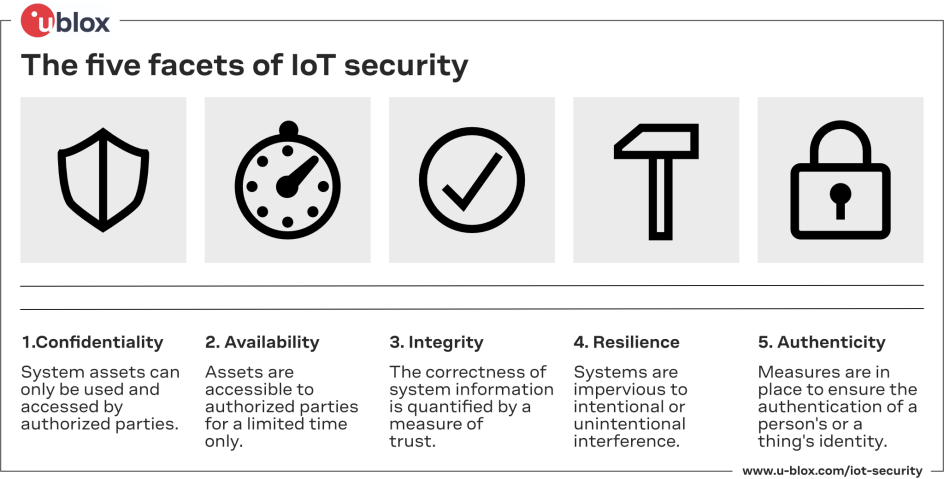
物联网安全的五个支柱
我们的解决方案、产品和服务整合了 u-blox 的五个安全支柱,将帮助您在当今的互联世界中保护您和您客户的业务。
1.安全启动
安全启动可确保物联网设备上运行的任何固件都是未经篡改的原装固件。具有安全启动功能的设备将仅启动和运行由原始设备制造商发布的受信任软件。
2.安全固件更新 (FOTA)
现场物联网通常需要定期升级以添加新功能并针对新出现的漏洞应用安全补丁。安全固件�更新可确保只能在设备上执行经过认证和验证的更新。
3.安全 API 和物理接口
安全 API 和物理接口可确保对设备的调试访问仅限于授权用户,API 的使用会经过身份验证。同时,该接口也将确保进出设备的数据的真实性和完整性受到保护。
4.安全传输层
传输层安全提供基于标准的加密协议,用于身份验证以及与服务器的签名或加密通信,保护传输中的数据以防止设备到服务器通信中的中间人攻击。
5.用于抗干扰和欺骗的鲁棒性
物联网设备容易受到蓄意的射频干扰。功能丰富的 GNSS 卫星信号、射频信号处理、嵌入式软件开发和数据加密,支持对空中接口的潜在攻击的检测,并提高了用于对抗 GPS 干扰和欺骗的鲁棒性。