- Short range radio modules
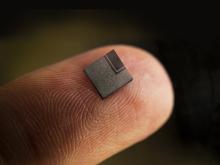
- Positioning chips and modules
u-blox Products
- Product selector
- Previous generations
- Contact sales
Find products
- Support portal
- Evaluation Kits and partner products
u-blox Support
- Product documentation
Documentation
- Investor relations
Investor relations
Insights
|
26 Jun 2020
IoT security: Innovation on all fronts
Emerging technologies promise to bolster IoT security at every level.
This article is an extract from our latest u-blox magazine on IoT security. Download your own copy of the magazine today!
The IoT is a complex organism. On one end of the spectrum, it comprises billions of data-gathering, functionality-enabling IoT end-devices deployed the world over in homes, cities, vehicles, factories, and just about anywhere else. On the other end is the cloud, a network of data centers distributed across multiple continents, where data are stored and processed, often using artificial intelligence algorithms to reveal otherwise hard-to-gain insights.
This simplistic breakdown overlooks the many technological layers required to make the IoT what it is. End devices host a large number of hardware components and sensors, potentially leveraging signals emitted by distant satellites or nearby radio beacons. Typically, they transfer data – often encrypted – to the internet over wireless short range (e.g. Wi-Fi and Bluetooth) or cellular (e.g. 4G LTE, 5G) communication technologies using one of many data transfer protocols.
To gain meaningful insights from the devices or to save resources, these data can be processed on the device (the edge), in the cloud, or somewhere in between (the fog). Ultimately, the data is integrated into some kind of cloud-based platform or other backend solution, where it can be accessed, leveraged, and shared with other users.
Every step in this process lends itself to varied approaches geared at increasing the security of the overall system. In this article, we’ll explore a selection of emerging technologies that promise to bolster the security of IoT applications, from the incoming radio signals they harness to the encryption solutions they use all the way to the distributed ledgers where the data might ultimately be stored.
Safer signals
A growing number of IoT devices – asset trackers, smart watches, drones, to name a few – rely on location information, typically determined using satellite-based positioning technology. But GNSS (Global Navigation Satellite System) signal jamming and GNSS receiver spoofing have become the technology’s Achilles heel, slowing down its adoption while data gathered using these devices could play an increasingly vital role in often mission-critical applications. Highly autonomous vehicles are a case in point.
A number of innovations are increasing the reliability of GNSS positioning solutions. For one, Galileo, the European GNSS constellation, has implemented a long-awaited signal authentication service (Open Signal Navigation Message Authentication, OSNMA), which it has announced should become available in 2021. By emitting signed messages, GNSS receivers and the applications they enable can be sure that they are working with valid signals, making it much more difficult to spoof GNSS receivers unnoticed.
Moreover, today’s modern GNSS constellations emit signals in multiple frequency bands that the latest generations of receivers are designed to track. In addition to dramatically improving the accuracy of GNSS position estimates from several meters to the order of one meter (or much lower using GNSS correction services), the redundancy these signals offer further increases the difficulty of spoofing GNSS receivers without being detected.
Better protocols
IoT devices are designed to operate under extremely tight constraints in terms of size, price, battery power, and bandwidth. Squaring these with demands for high security has been challenging, as conventional encryption methods tend to considerably increase the size of the data payload that the devices have to transfer. Because data transfer is the most power-hungry process in most IoT devices, encryption thus comes at the cost of reduced power-autonomy.
Recently, a new lightweight security protocol specifically tailored to the needs of such power-constrained use-cases has been gaining traction. Defined by IETF (the Internet Engineering Task Force), OSCORE, which is short for Object Security for Constrained RESTful Environments, offers a number of improvements in securing messages sent using CoAP (constrained application protocol), one of the preferred communication protocols used in LPWA (low power wide area) use cases.
First, it only encrypts the sensitive part of the data payload, which is the data reducing message size cutting down bandwidth requirements, and saving power. And because metadata, such as the destination, is not encrypted, the encrypted message can be relayed all the way to its destination without ever revealing itself. Second, OSCORE uses pre-shared keys rather than the conventional, and significantly more resource expensive, key negotiation process, offering messages sizes down to a dozen bytes - ideal for typical LPWA use cases. It looks good on paper. But the jury is still out on its success, both in terms of adoption and the actual security it offers in the field.
AI AI AI
Just as artificial intelligence and machine learning are offering new ways to gain important insights from highly complex data, the technologies are offering new tools to improve IoT security. By training a machine learning algorithm with data on the bandwidth a device uses during normal operation, it can learn to recognize – and flag – abnormal behavior that would otherwise be overlooked. To save computational resources and battery power, these algorithms can be trained on the cloud and disseminated to hundreds or thousands of deployed IoT devices using a firmware-over-the-air update.
AI can also play a new role in securing connected systems at much grander scales. Across industries, smart cities, and other use cases that leverage the IoT, digital twins are gaining in importance. As virtual representations of the physical system the devices are deployed in, digital twins offer a virtual platform to monitor and optimize the performance of real-world systems. But it doesn’t have to stop there.
Rather than leaving the fine-tuning up to human security architects, the security engineers could let two artificial intelligences play cat and mouse: As one AI continuously improves the security of the overall system, the other one comes up with more and more devious attacks to thwart its defenses. In the same way that Google’s AlphaGo taught itself to play Go at a super-human level, the resulting security architecture could dramatically outperform that of a human-designed system.
Better than the blockchain
Two years after the Bitcoin bubble famously burst, the Blockchain and other distributed ledger technologies (DLT) have all but disappeared from newspaper headlines. But behind the scenes, startups and industrial associations are hard at work looking for ways to leverage these technologies’ unique benefits. DLTs offer a highly transparent way to keep track of transactions, assets, or steps in an industrial process chain. By running highly autonomously, they can be faster, cheaper, and less prone to failures than more conventional forms of record keeping.
DLTs also offer a number of security-related benefits. Because the data is distributed across countless computers and servers, altering records stored using a DLT is extremely difficult. Data can easily be stored in encrypted form, allowing access to individual records to be tightly restricted. To cite but one example of how the technology could be used: DLTs have been proposed as a secure vault for health data, protecting patient confidentiality, and putting individuals in full control over who receives access to their data and when.
While the Bitcoin was a glutton in terms of its power consumption (the Blockchain was once estimated to use more electricity than Switzerland with its eight million inhabitants), other DLTs offer similar benefits with only a fraction of the power demand. But given the novelty of the technology and a number of challenges, such as ensuring the accuracy of data stored in a DLT, it may still be several years before DLTs begin to live to up the hype they generated in 2018.
Shoring up – and shaking up – security
The technologies driving improvements in IoT security are rapidly advancing on multiple fronts. Artificial intelligence, next generation data encryption and key management approaches, advances in secure hardware, and new solution architectures are increasing the sophistication of IoT security approaches, ultimately making the lives of those seeking to compromise them more difficult. Decades of experience in IT have shown that security progresses similarly to the cat and mouse game described above: It’s a continuous arms race that is rapid improves the security of leading IoT technology, benefiting product managers and end-users alike.